
October 2023
Subject: Question about Svalbard and seedbank protection status quo.
To: firmapost@sysselmesteren.no,
Cc: Stefan Schmitz @croptrust.org, Sigurd Lunde @statsbygg.no , cab-breton @ec.europa.eu
Dear Lars Fause,
Would
you like to have a informal chat about why the protection of Svalbard
government vital infrastructure and *probably also the seed bank, is
still lacking some basic protection measures against espionage and
sabotage?
But more importantly how you personally can make sure
that the Svalbard district under your supervision, does get its
protection in decent order to prevent ongoing espionage and potential
sabotage..
This isn't a sales pitch, nor is it politically
motivated. It's merely about findings from a long term research project,
sharing useful findings information for the benefit of the population.
It's not a pleasant subject of course, and in itself also a wasps-nest to even mention the subject.
Especially
since the 2010 news-media publications about Norway's DSS and Nasjonal
sikkerhetsmyndighet and Other 'security services' clear failure to get
their act together on infra protection, ..and the consequent blatant
continuation of ostrich-politics which caused the problems to start
with..
Which brings us to 2023 (10+ years later) whereby it is
publicly visible that Norway govt still has not managed to even
implement several essential basic protection measures, but instead has
continued (like gophers undermining the area) with adding more and more
odd access options with internet connections which fail to even comply
with known mandatory security standards, and.. still leaking a steady
stream of sensitive internal information to the outside and thus also to
hostile actors.
The reason why the Norwegian security
services, (just like many other governments), don't get their act
together, to even enforce only 3 most essential very simple to implement
security rules, ..is that there is a Catch-22 in their chosen
method{*1}.
Which in effect means that they rather turn a blind
eye on ICT related projects which clearly are Not compliant with
official security policies. This continues to happen large-scale because
the individual functionaries don't want to make a fuzz about
wrong/(even illegal) choices made by ivory tower style govt IT projects.
*
After all, those 'security' functionaries do Not get paid a cent more
if they bother to have the courage to tell those (fellow govt employees)
IT projects people to stop ignoring some of the security regulations.
In contrary, those 'security' functionaries do risk getting their
careers hampered as a result of "getting in the way" of prestigious IT
related projects by those who make a very lucrative profit from those
projects and the (backstabbing) power influence that comes with it. As
you probably know ;-)
So far a bit of background
information on why Nasjonal sikkerhetsmyndighet/Departementenes
sikkerhets- og serviceorganisasjon can't even decently protect their own
classified data handling and control infrastructure, ..so they stand no
chance of taking "care" of the State Vital Infrastructure, as has
become rather obvious since 2010 and after.
This next
section contains only a few specific details which may be outside your
field of knowledge. But by reading it all you do to get a bit of a
picture about context and something specific to chat about with your
colleagues.
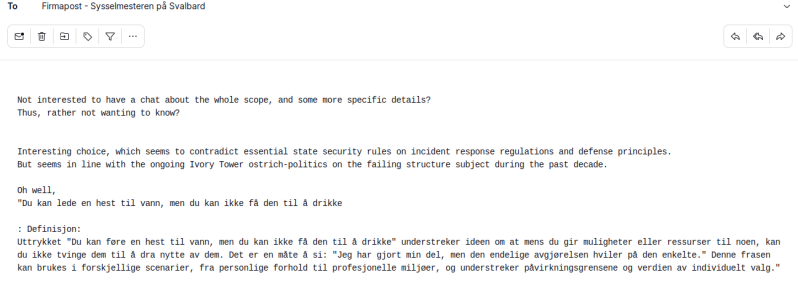
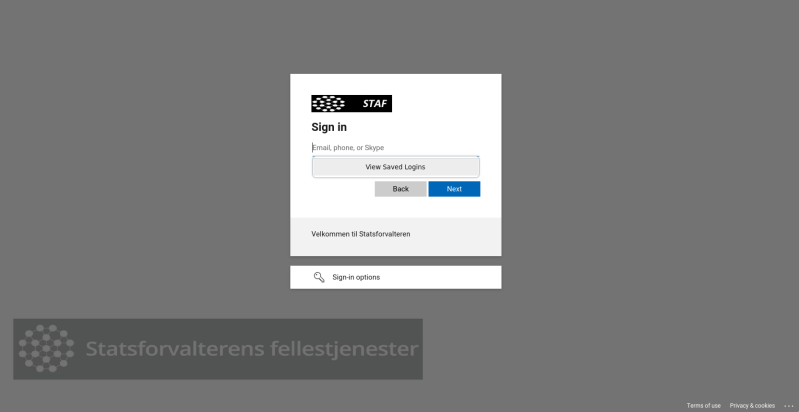
# A very simple and telling example has been added
in the form of a picture of an access path to a govt system of which
there are many with similar issues. A picture which shows a thing or two
about how projection of systems like *prod.sysselmesteren.no and the
rest of the infrastructure is done rather carelessly &
lazy/incompetent.
Simple fact is: That such an 'public' access
path should never have been allowed by 'security' services, to even
exists! And besides that, the system owners should not have been allowed
to 'advertise' various bits of information about it and its structural
flaws. Therefor "SMS724.sysselmannen.svalbard.no,S4ZX790" and others are
visible.
Since there is "no need" at all for it to be even
approachable by hackers, curious students or those known hostile actors,
who seem currently ''allowed'' to use all kinds to child's-play
trickery to gain access without it ever being noticed by the owners of
those back-end govt systems nor by those govt security services having a
clue about what is going on outside their field of view under the
radar. The extra Cloudflare 'security' -external- service in between, in
fact makes it even more vulnerable because it obscures some key events
from view, sadly.
Especially, since making foolproof sure that
only very specific authorized and identified people can have access, is
in fact a simple matter of applying just 2 of the 3 rules, which makes
absolutely sure that unwanted visitors can't even find ways to gain any
form of access to those systems and data. [technical and procedural
details can be shared in confidential conversation]
Observation:
Svalbard/Spitsbergen has a relatively small inhibited area, with few
people and very little digital/computer infrastructure per square mile
of the whole geolocation area. Most of the key digital infra is located
remotely in Norway and some other countries far away.
But
Svalbard at the same time is a location where The seed bank is located,
and also a prime target of .ru unwanted strategic attention the past
years, it seems...
Now for a more pleasant subject: a way forward.
It
is in fact rather simple to make absolutely sure that unwanted
digital/cyber 'visitors' can not even get close to sensitive information
and control systems.
Not only those few systems and which are located locally, but also those located in mainland Norway.
The
only thing that actually needs to be done, is rigorously enforce 3
specific basic security rules! (which the 'security' services have
clearly failed/neglected to do so the past 2 decades.)
There is no need at all for any extra investments, or products, or services, or complex methods, or extra policies.
~ All that is actually needed, is factual strong "enforcement" of just 3 common sense rules.
1. Keep IT simple s.... (KISS principle)
2. "Need to know" principle
3. "Integrity Safeguard" principle.
Those
3 most elementary age old rules as stated above, are boiled down and
paraphrased core values, which have been described in far too
bureaucratic over-complex texts in most official security policies and
standards like ISO27001, etc. So those core rules are not clearly
visible nor emphasized in those far too bureaucratic current policies
and standards, because the essence has been lost in the overwhelming
listings of various sub-details and administrative focus which had
derived from those more sensible core principles as far back as the
1980's as in "DoD 5200.28-STD aka Orange Book".
So...
focusing on just those 3 core rules, and enforcing them resolves the
current cyber-vulnerabilities problem for just our vital
cyber-infrastructure and also those connected physical restricted area
access security systems.
This may sound far too simple and
easy, to believe that that is all it takes to ensure that hostile actors
can no longer get access to those sensitive data handling systems and
stop the ongoing blatant sensitive data leakage/breaches which the
Norwegian govt has been unable to prevent due to a Catch-22 in its core
management structure.
Any "Egg of Columbus" solution can be
substantiated just as easy, ..but as with the Egg story, it can only be
understood "if" you are willing to witness how it the puzzle is solved,
to see it for yourself and then grasp the full context of the initial
problem context dilemma, and thus also its natural logic solution.
It's not rocket science, its about simple common sense logic and thinking outside the box.
So the key question is:
Lars,
do you as current Governor, want the Svalbard/Spitsbergen sensitive and
classified data and infrastructure to be defended properly against
hostile actors and stop the data leakage/breaches ?
_ If not, why not?
_
If so, lets meet in person and learn how it can be done, in order to
put a very simple foolproof Safeguard structure actually in place. Then
you can use that essential knowledge yourself to make things happen to
ensure a more decent defense structure for the area under your
supervision.
Med venlig hilsen,
Snr security officer and researcher.
-------
Soapbox, Post Scriptum:
The
'security' and IT people who are 'responsible' for the infrastructure,
will almost certainly have many plausible Sounding excuses and use
various known forms of self-justification.
But the bottom-line
is: that they fail to actually live by sensible and govt mandatory known
rules and regulations, because it is still more lucrative for them
personally to ignore a few of those very simple rules, ...sadly.
Perhaps
a bit like some highly educated people who keep gobbling down sweets,
even after the hospital specialists told and showed them that they
already have type 2 diabetes and where in hospital because a few toes
had to be amputated due to predicted body system failures. Just like the
majority of state project people keep connecting key access systems and
odd gateways to the big bad global Internet, without bothering to first
making sure that they at least chose options with are proven to be
actually "secure by design" and tested to be fully compliant with
regulations.
Sadly, Instead they still keep choosing/allowing
various oddly popular products and methods which are notorious for being
endlessly "vulnerable!" (due to needless over-complexity and/or known
back-doors for espionage) like many of the systems chosen for the
Svalbard.no and the rest of the Norge's state infrastructure. All that
is clearly visible for those who bothered to have a look at the status
quo.
#{*1} # www.regjeringen.no/contentassets/c57a0733652f47688294934ffd93fc53/national-cyber-security-strategy-for-norway.pdf
Sadly
this key policy document is one of those many far too bureaucratic
publications, which has been criticized by experts for the policy an
Ivory Tower point of view on the subject, which is actually missing the
core essence of How to implement a functional structure!
Instead
the policy creators keep hanging on to long known to be a dysfunctional
dogmatic methodology. And they blatantly refuse to even openly debate
the overload of hard evidence against their dogmatic outdated method, in
order to become able to improve things. So they also chose to ignore
their own published "improvement cycles" principle which they themselves
advocate, know as (P.D.C.A. Cycles)
=> adding insult to
self-injury, that document itself is leaking sensitive inside
information to hostile actors and others. Which in itself is one of the
far too many symptoms of the elitist carelessness of those ivory tower
bureaucrats who keep being overpaid/Rewarded to produce such key
"policies" for a state during a time of ongoing cyber- and
physical-warfare.
When looking at the foolish self-serving
actions of those 'security' policy makers, there seem to be a lot of
similarities with "Kejserens nye klæder" by Hans Christian Andersen
1837, Doesn't it !?
--
2010:
"Dokumenter
og brev som dette dukket opp flere steder – og tegnet et bilde som tydet
på at detrett og slett var mye rot i DSS. Mange av brukerne – dvs
enkeltdepartementene – klaget med
jevne mellomrom."
-
"Eks.
4. Analyse av ekstern kommunikasjon i Depnett-UTil Finansdepartementet
fra FAD 09/1314 200800247-/JFN 14. mai 2009Rapport - Analyse av
ekstern kommunikasjon i DepnettU (417061).pdf
Dette var ett av de viktigste dokumentene som kom frem i postjournal-søkene var
knyttet til ”analyse av ekstern kommunikasjon”. Dokumentene var en del av
brevveksling mellom FAD og Finansdepartementet, O ED og UD.
Dokumentet refererte til en rapport som DSS hadde bestilt høsten 2 0 0 7 for ”å få et
dypere innblikk i risikonivået knyttet til internettrafikken inn til regjeringsfellesskapet”.
Dataskandalen i regjeringskvartalet"
etc..
etc...
---
* www.sysselmannen.svalbard.no
inetnum: 217.17.216.128 - 217.17.216.255
netname: NO-NORGE-NET
descr: the Gateway to the public sector in Norway
mnt-by: KAPASITET-NO-HM-MNT
route: 217.17.208.0/20
descr: Sognenett AS
origin: AS31169
created: 2004-06-10T06:52:14Z
last-modified: 2013-06-18T08:31:04Z
etc..